Tuple supports SAML Single Sign-On as part of the Standard and Enterprise plans. SSO lets your team authenticate through your identity provider instead of managing separate Tuple credentials.Documentation Index
Fetch the complete documentation index at: https://docs.tuple.app/llms.txt
Use this file to discover all available pages before exploring further.
Provider-specific guides
Okta
Includes optional SCIM provisioning
Google Workspace
Google Admin console setup
Microsoft Entra ID
Formerly Azure AD
OneLogin
SAML Test Connector setup
General SSO setup
If your identity provider is not listed above, you can configure SAML SSO manually using the values below.Email addresses in and Tuple must match exactly. For example,
dev+tuple@company.com does not match dev@company.com. Verify your team’s email addresses before enabling SSO.What you need from your identity provider
- Your SSO IdP Entity ID
- Your SSO target URL that performs authentication
- Your auth certificate or its SHA1 fingerprint
- Attributes that include
first_name,last_name, andemail
Tuple’s SAML endpoints
| Field | Value |
|---|---|
| Entity ID | https://production.tuple.app/users/saml/metadata |
| Assertion Consumer Service (ACS) URL | https://production.tuple.app/users/saml/auth |
Enable SAML in Tuple
Navigate to the Settings tab of the team management dashboard.Only team owners can enable SAML. To find out who your team owner is, check your profile.
Managing your SAML configuration
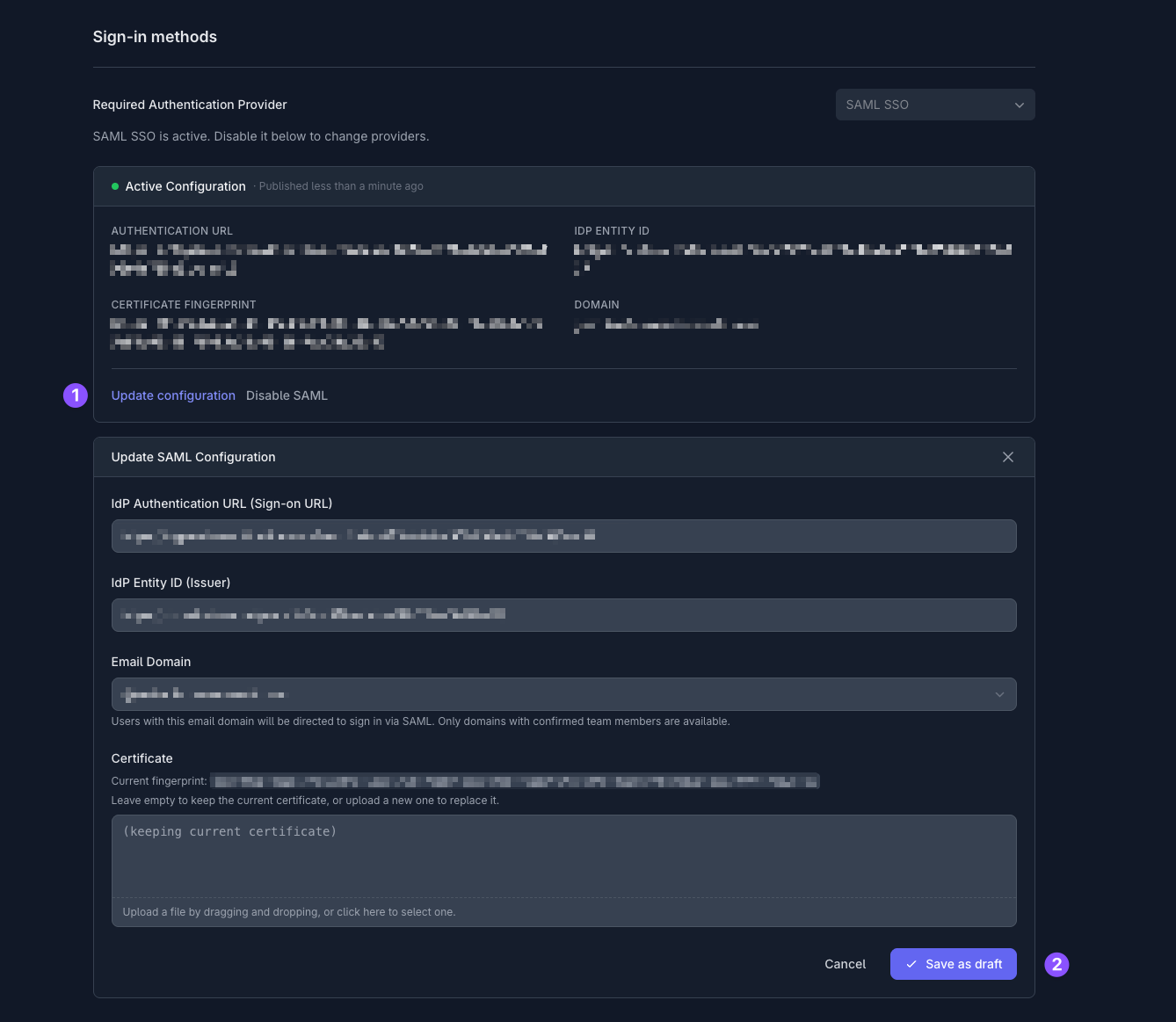
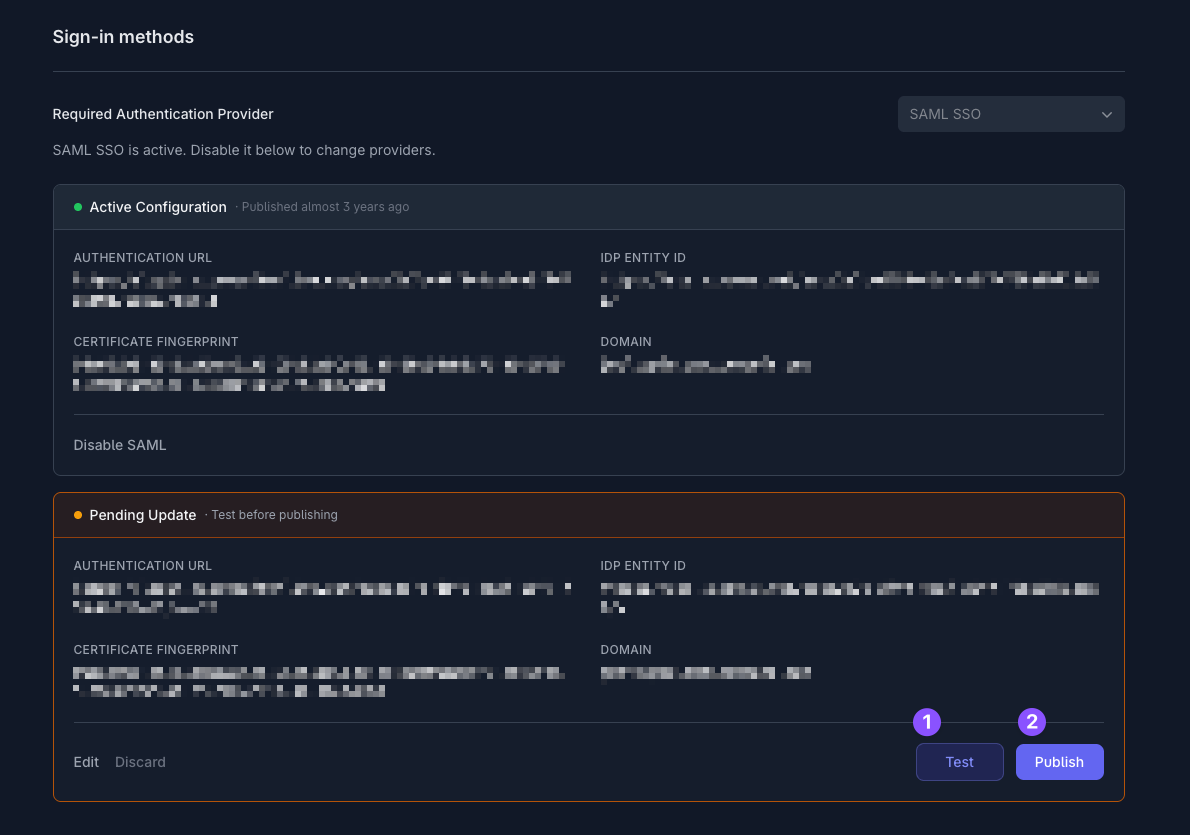
Tuple keeps a single Active Configuration plus any Pending Update draft you’re working on. Changes are staged as drafts so you can test them before they affect the rest of your team.Update an existing configuration
On the Settings tab of the team management dashboard, click Update configuration on the Active Configuration card. The Update SAML Configuration form opens pre-filled with your current values. Leave the Certificate field empty to keep the existing certificate, or upload a new file to replace it. The current fingerprint is shown above the upload field. Click Save as draft to create a Pending Update. From there, Test the draft, then Publish it when you’re ready. You can also Edit the draft to make further changes, or Discard it to throw it away.Archived configurations
When you publish a new SAML configuration, the previous one is automatically archived. Expand archived SAML configurations on the Settings tab to see past configurations: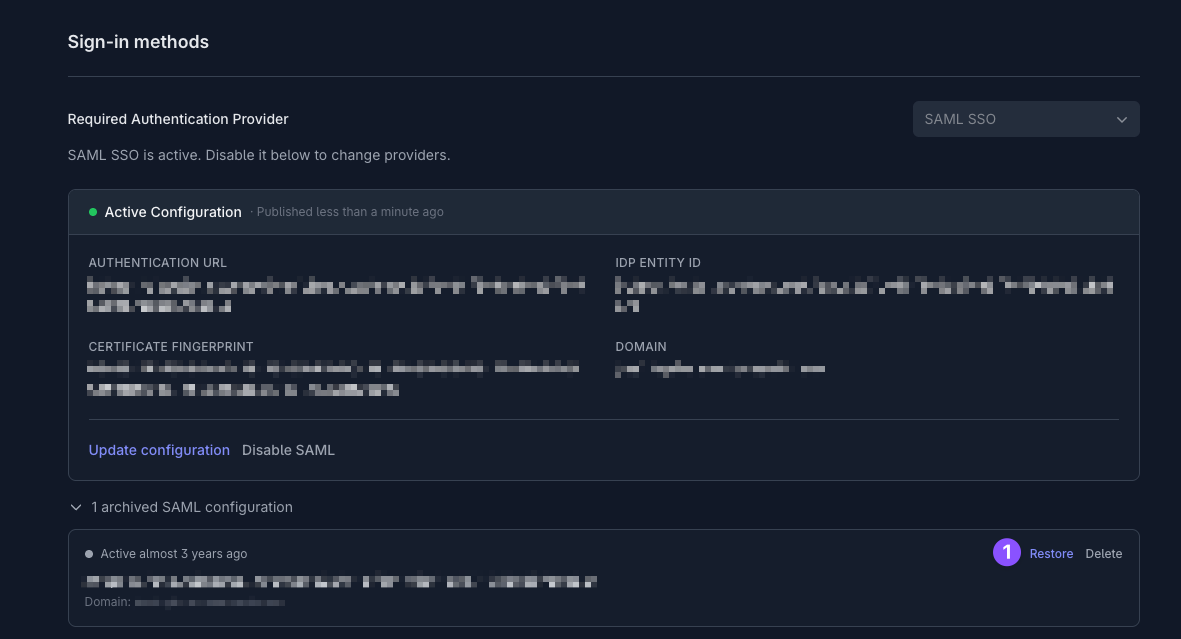
- Restore — bring an archived configuration back so you can test and publish it again. This is useful if you need to roll back to a previous identity provider setup.
- Delete — permanently remove an archived configuration.
Reference
Provisioning and deprovisioning
Provisioning and deprovisioning
The first time a user authenticates through your identity provider, Tuple provisions an account for them. If you are on a per-seat billing plan, billing begins for that seat immediately.You can disable a user’s access in your identity provider, but deprovisioning their Tuple account (and stopping billing for that seat) must be done on the team management page by your team owner.For automated provisioning, see SCIM provisioning.
Roles and permissions
Roles and permissions
Tuple has three roles: team owner, team manager, and user.
- Team owners can manage team settings, add and remove users, promote managers, and update billing information.
- Team managers can manage team settings, add and remove users, and promote other managers.
- Users can make and receive calls and share team invite links.
Email requirements
Email requirements
Email addresses in your identity provider and Tuple must match exactly. For example,
dev+tuple@company.com does not match dev@company.com. Verify your team’s email addresses before enabling SSO.
