Email addresses in and Tuple must match exactly. For example,
dev+tuple@company.com does not match dev@company.com. Verify your team’s email addresses before enabling SSO.Add a custom SAML app
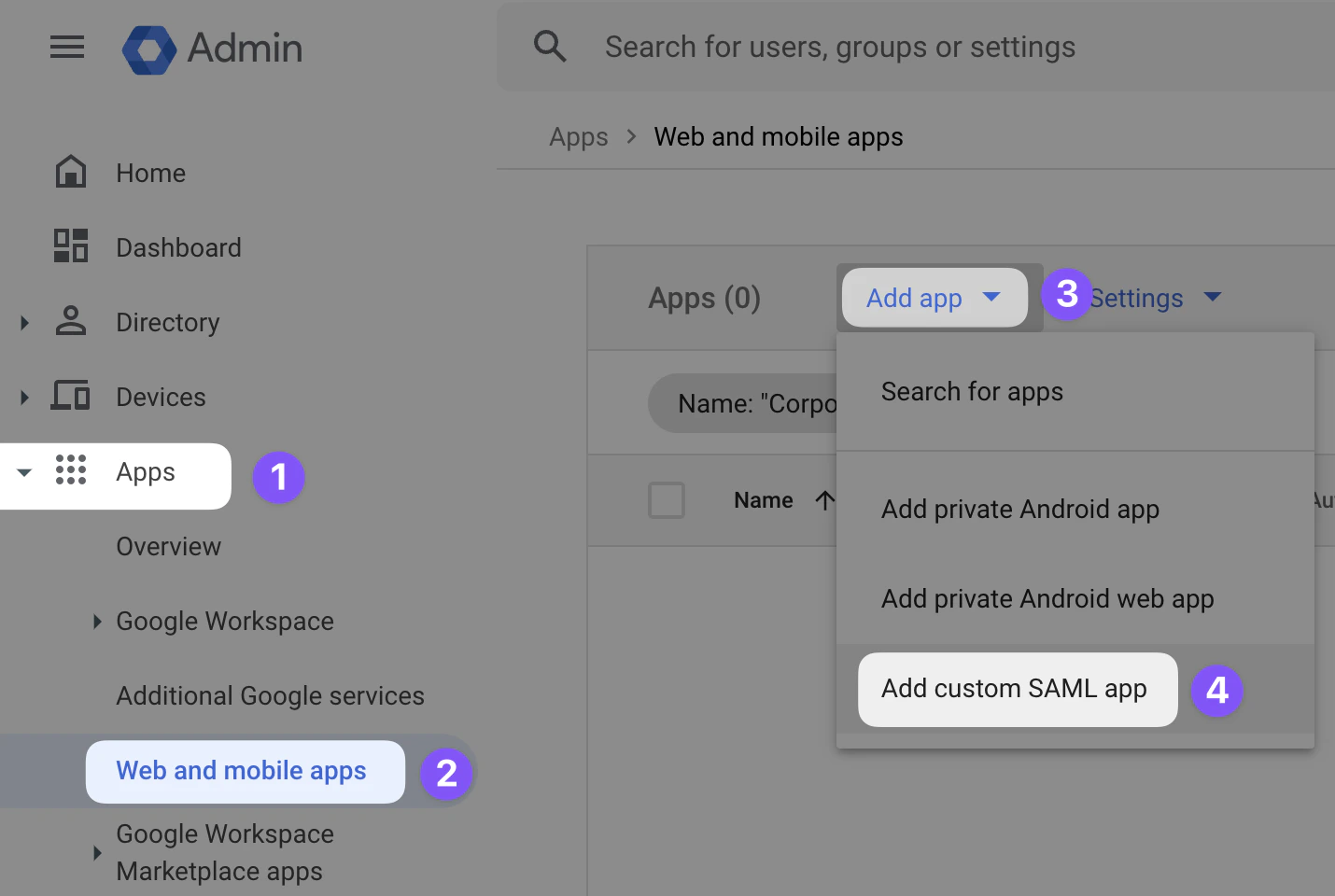
Sign in to your Google Workspace Admin console. Navigate to Apps > Web and mobile apps > Add app > Add custom SAML app.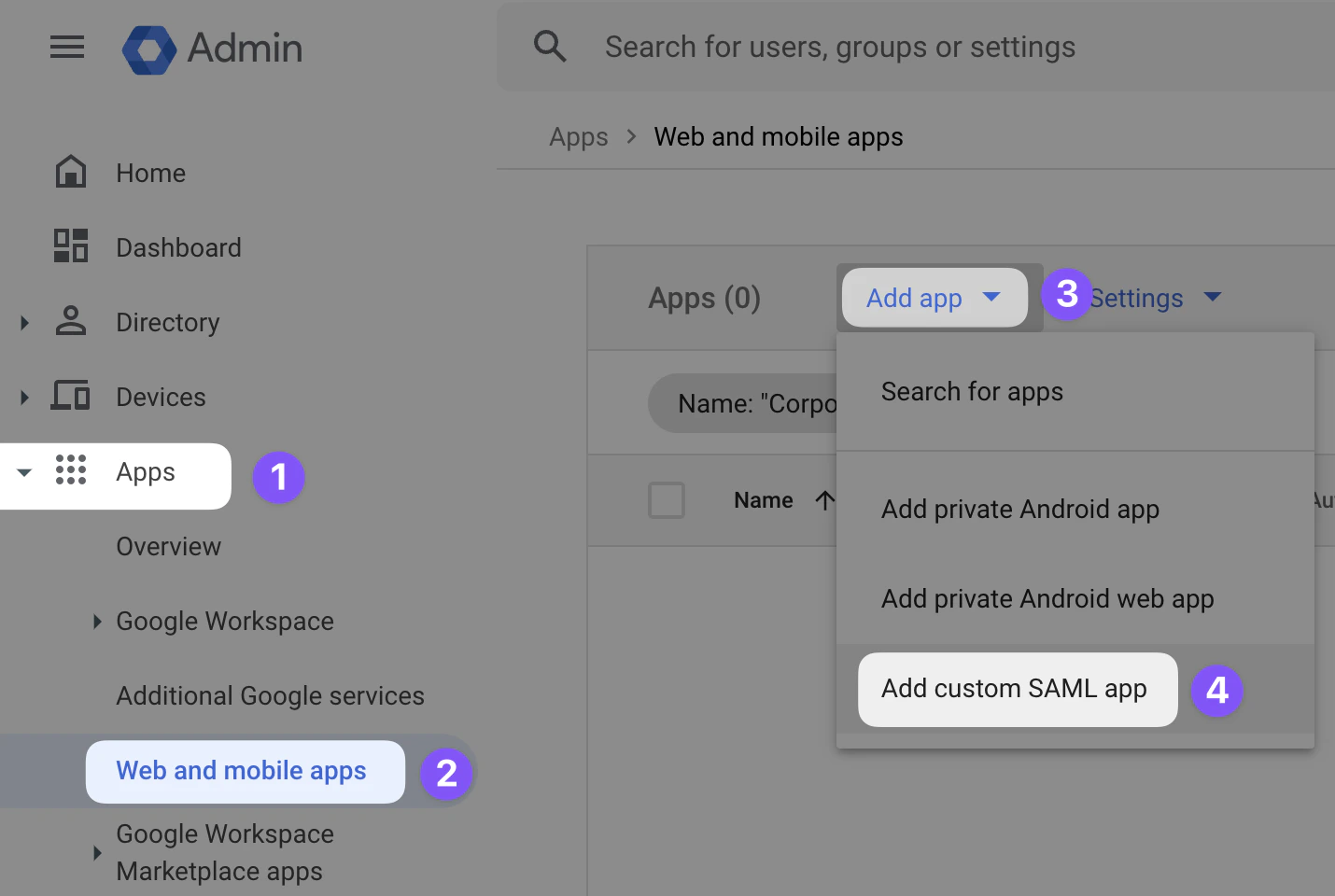
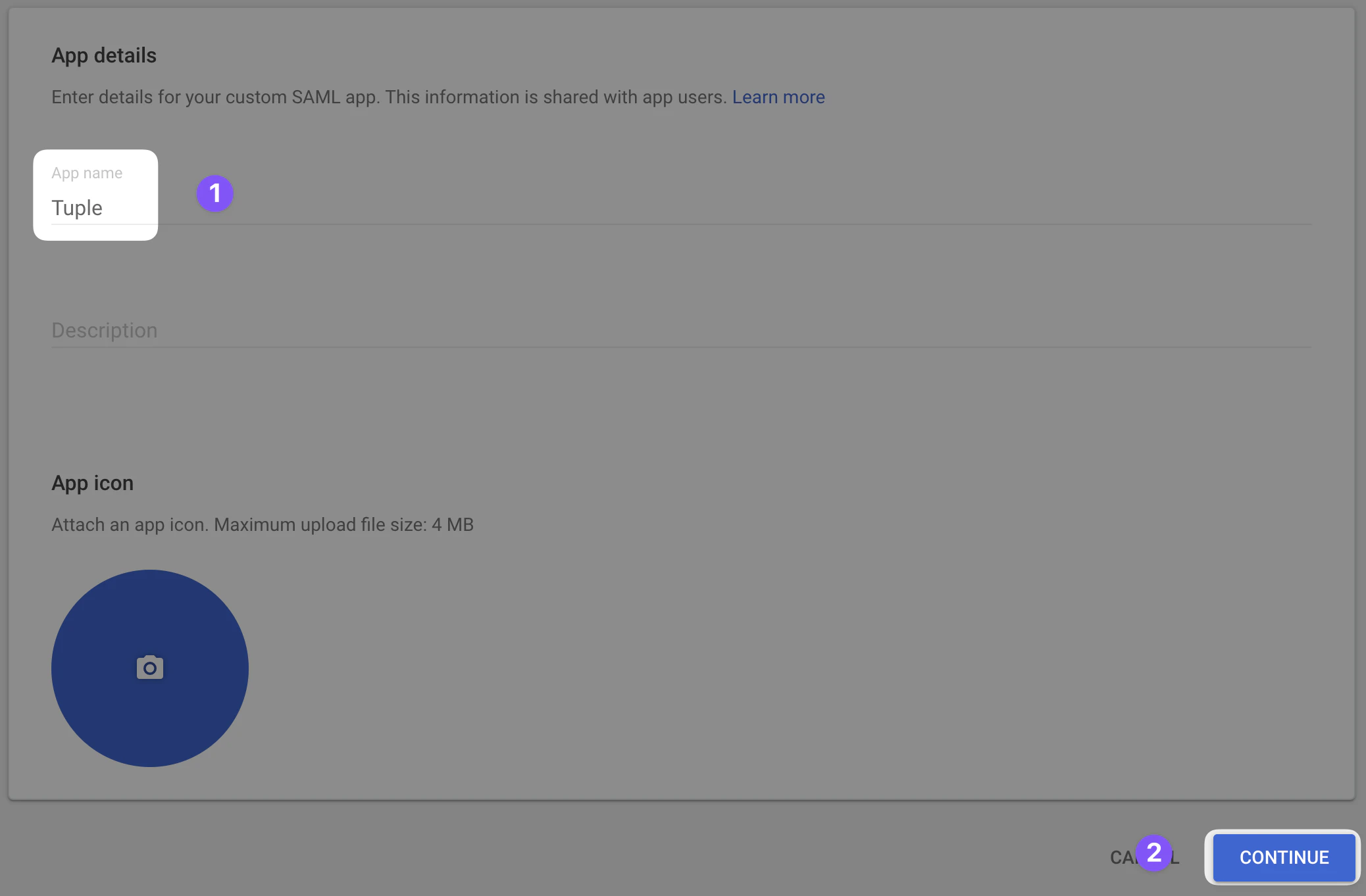
Create the app
Name the app “Tuple” and optionally upload an icon, which you can download here.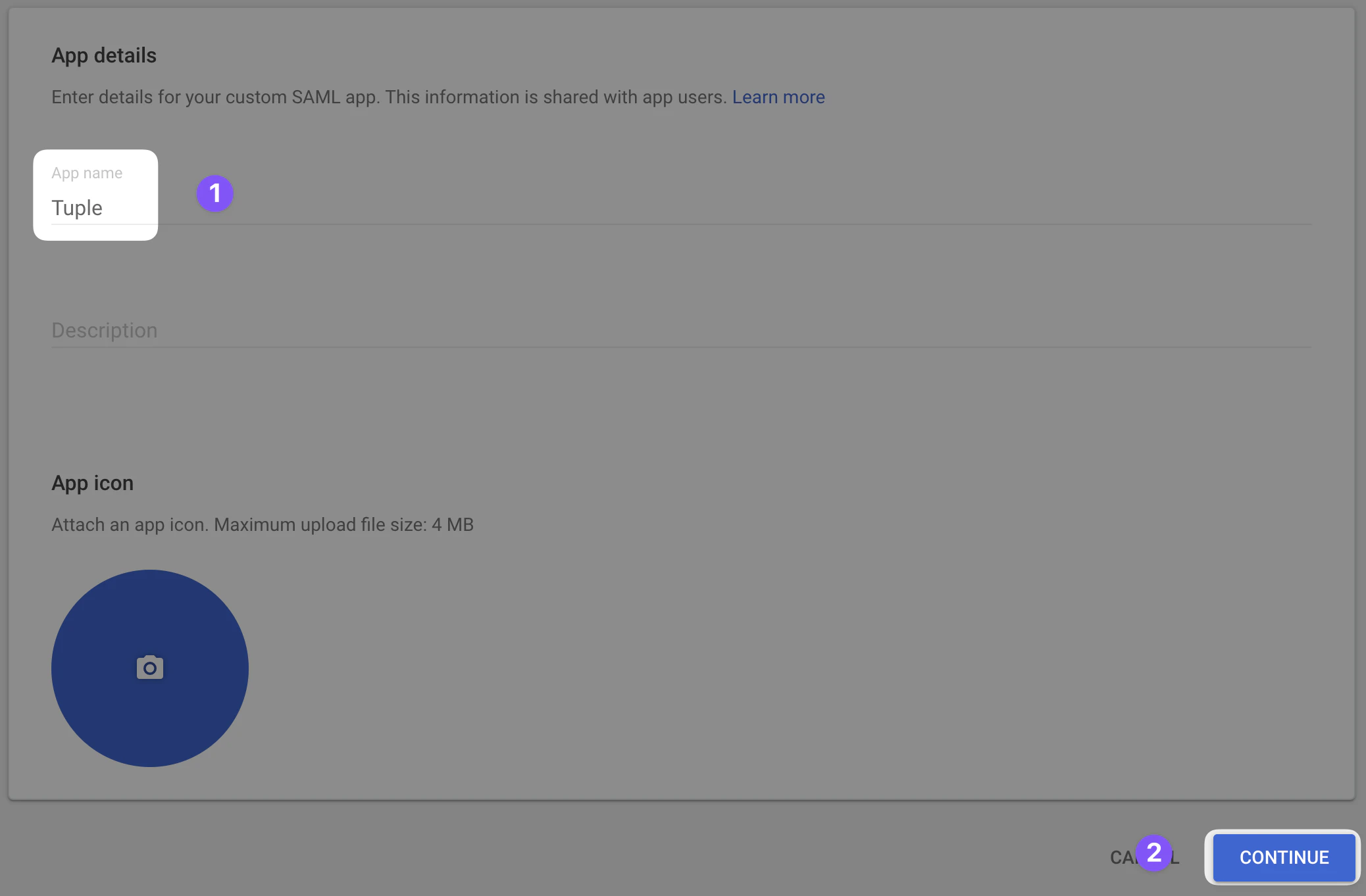
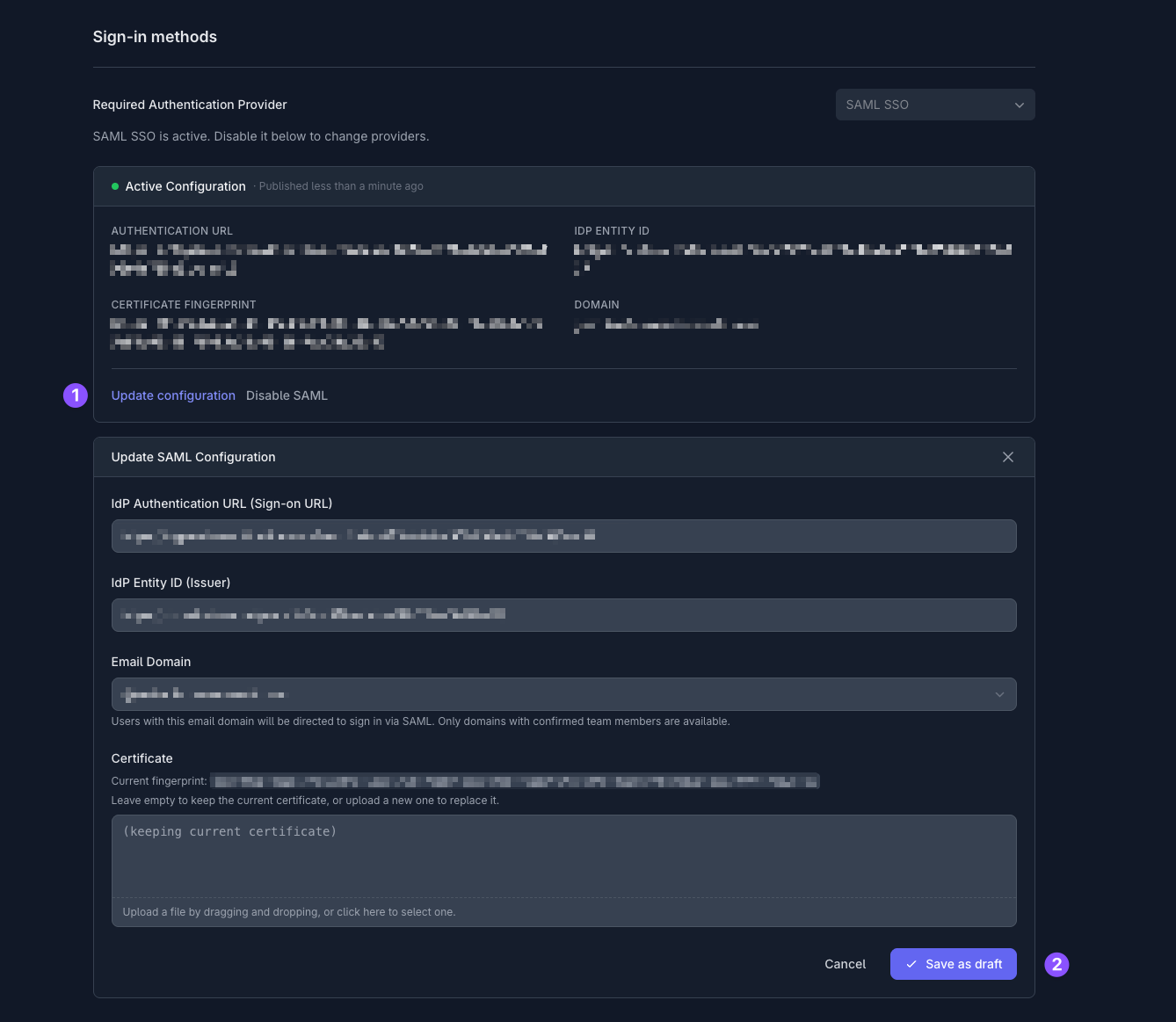
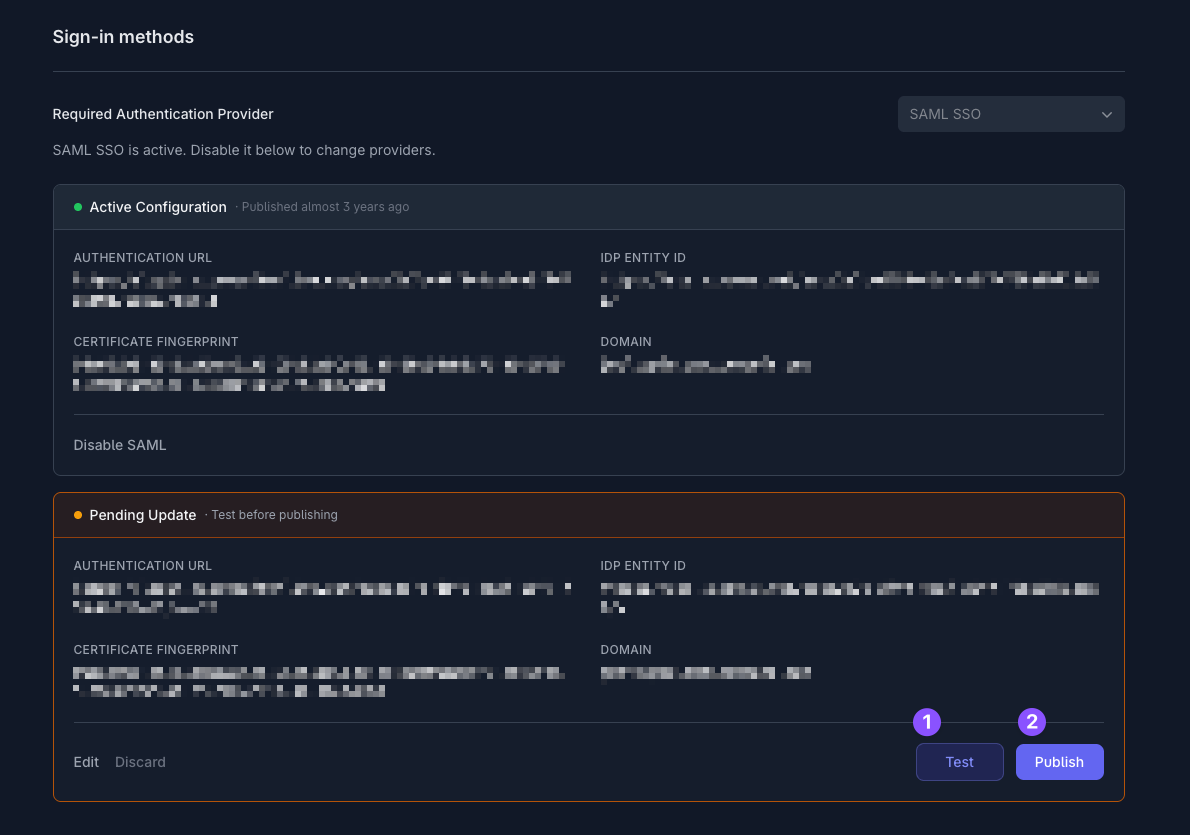
Configure your Tuple account
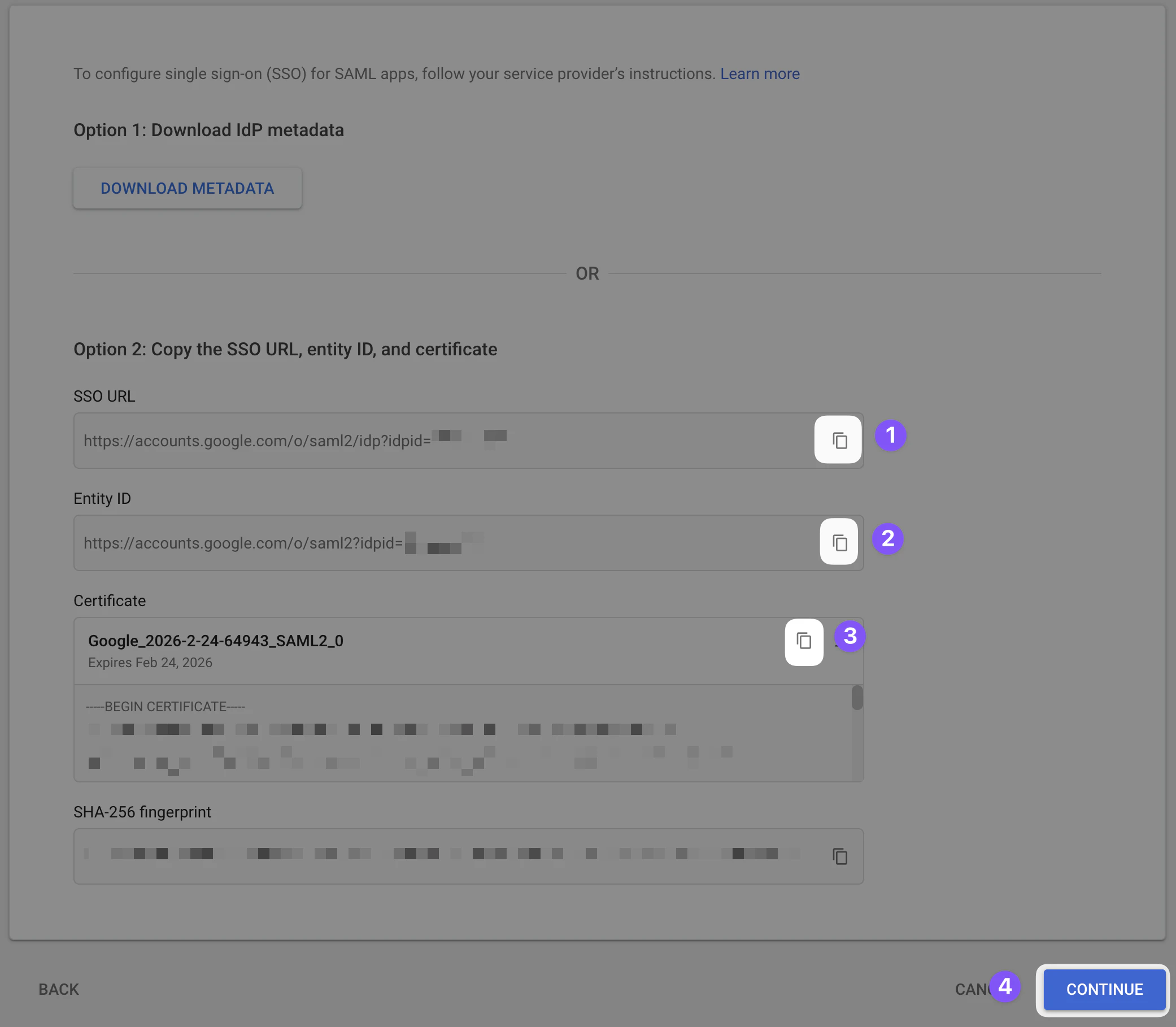
You are shown the Google Identity Provider details. Copy the values from this screen: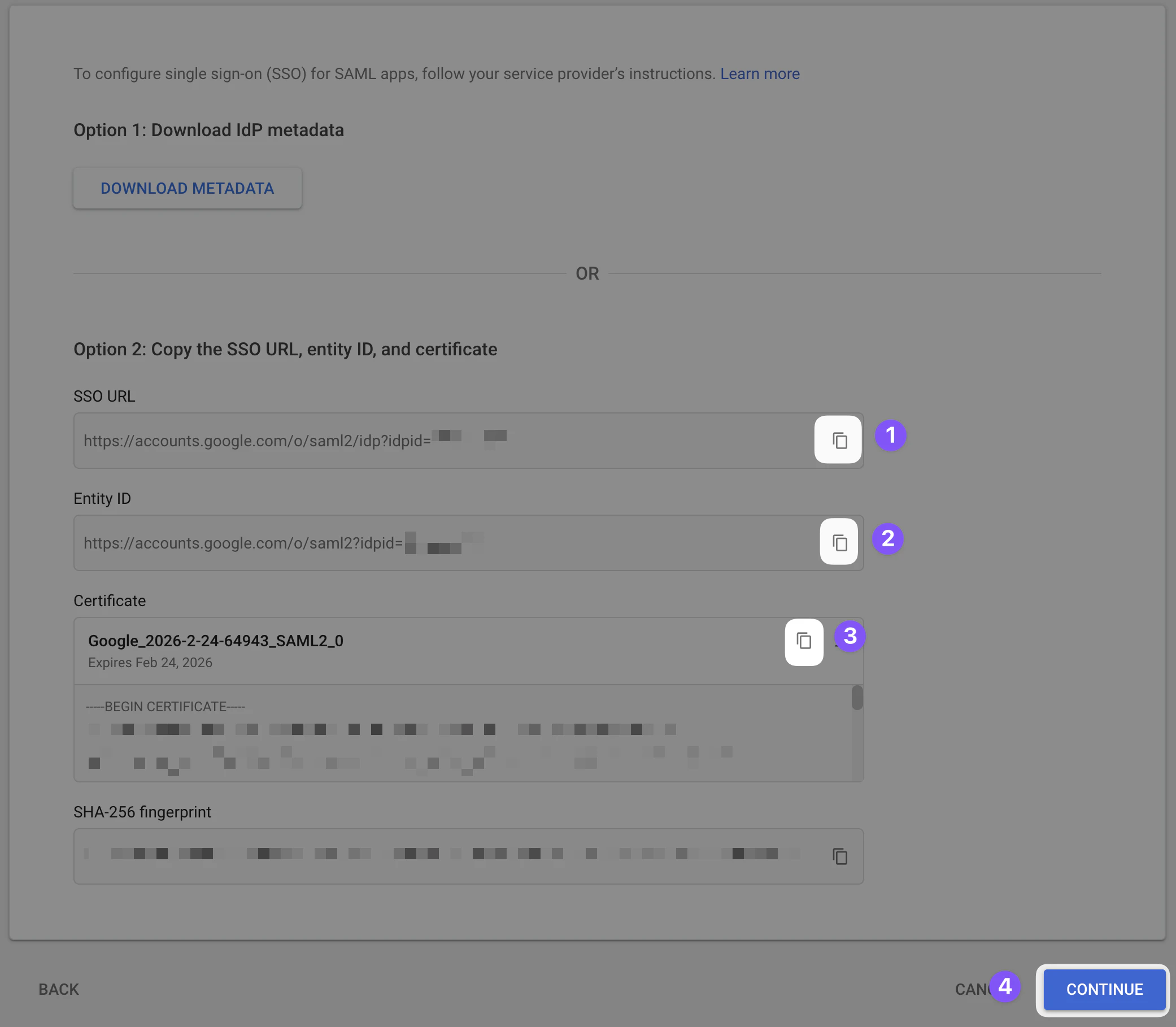
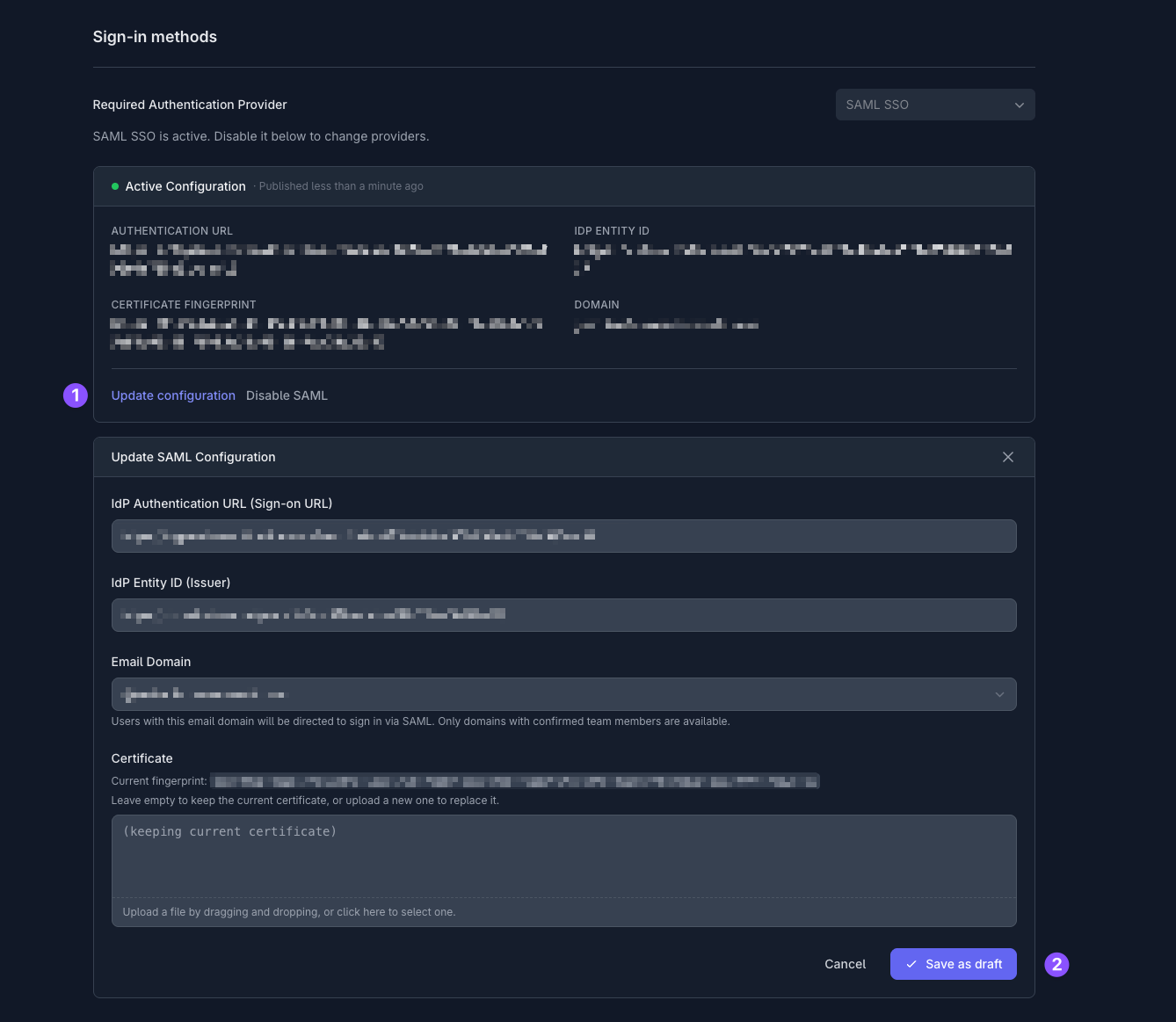
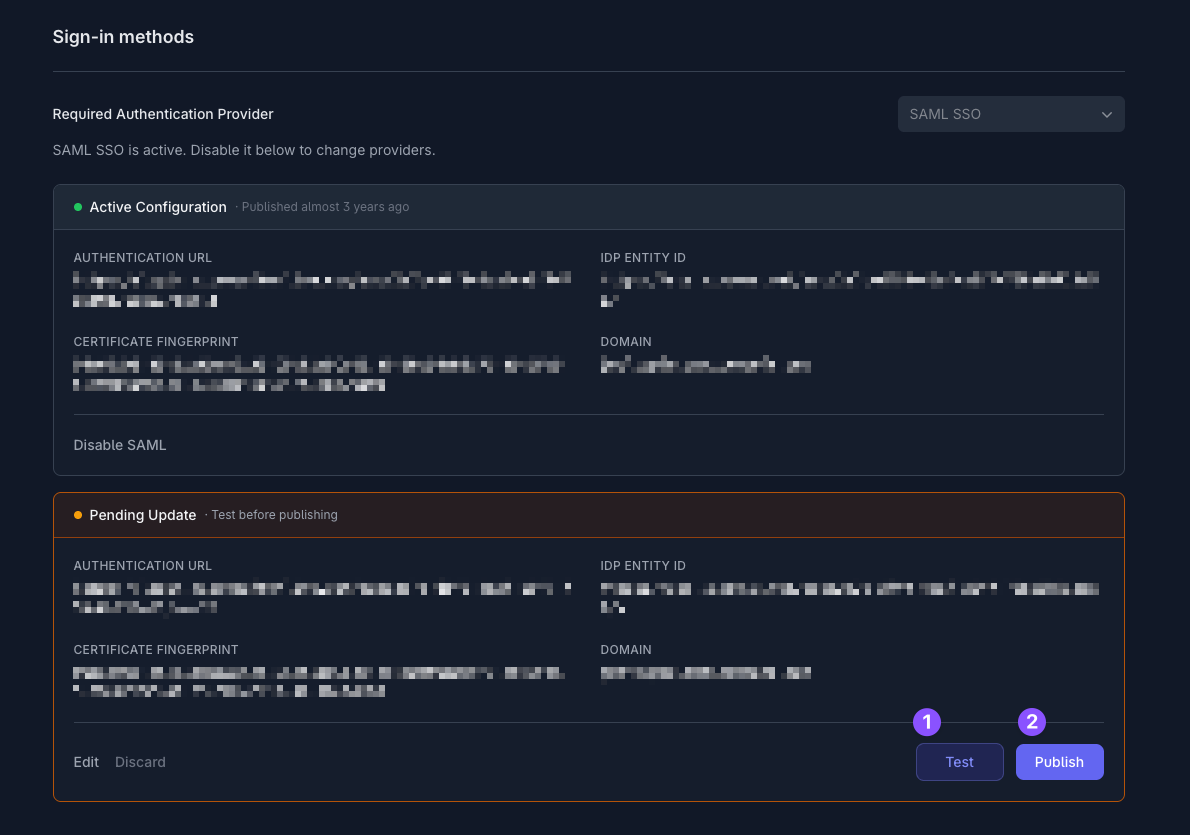
Only team owners can enable SAML. To find out who your team owner is, check your profile.
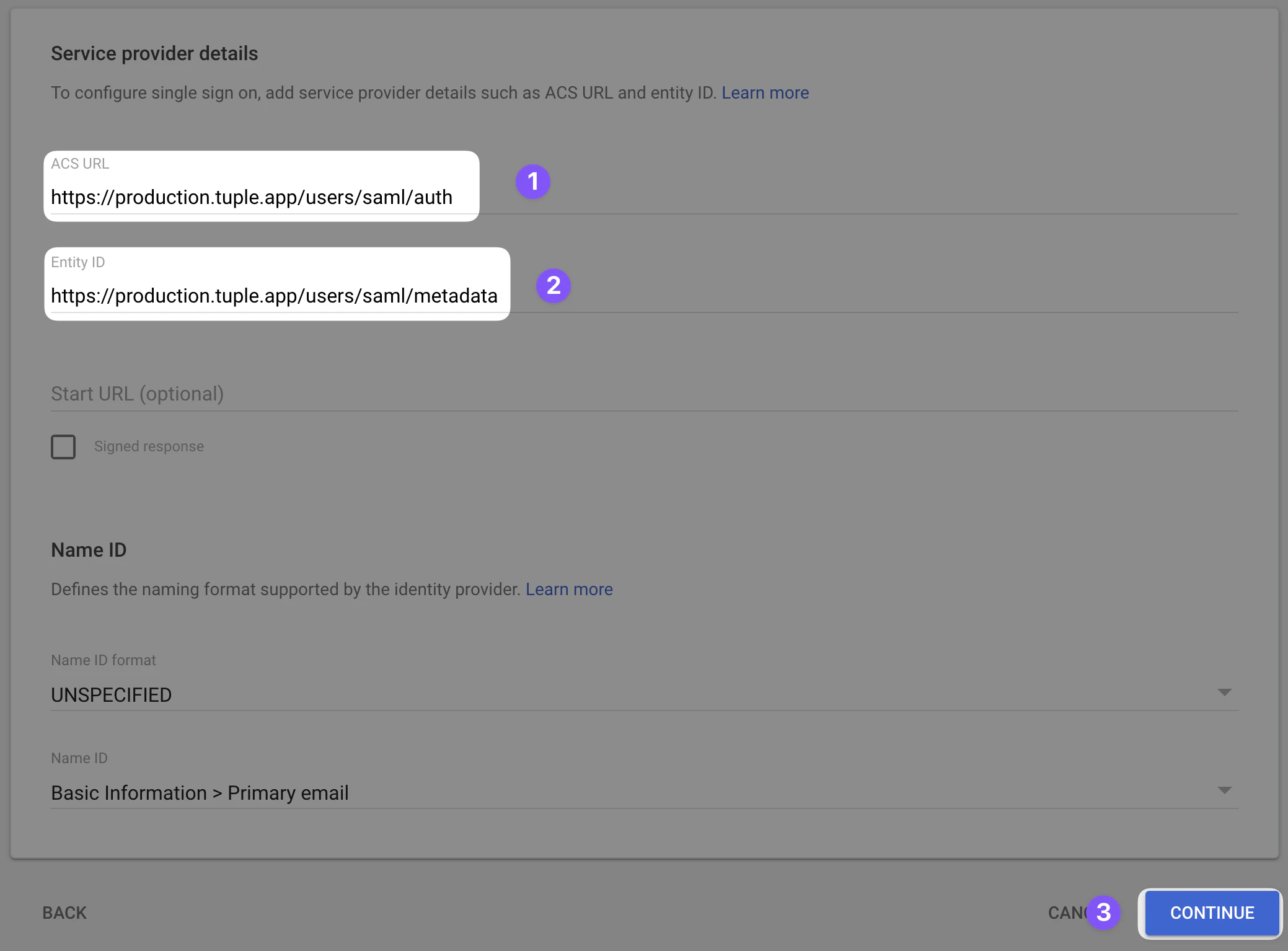
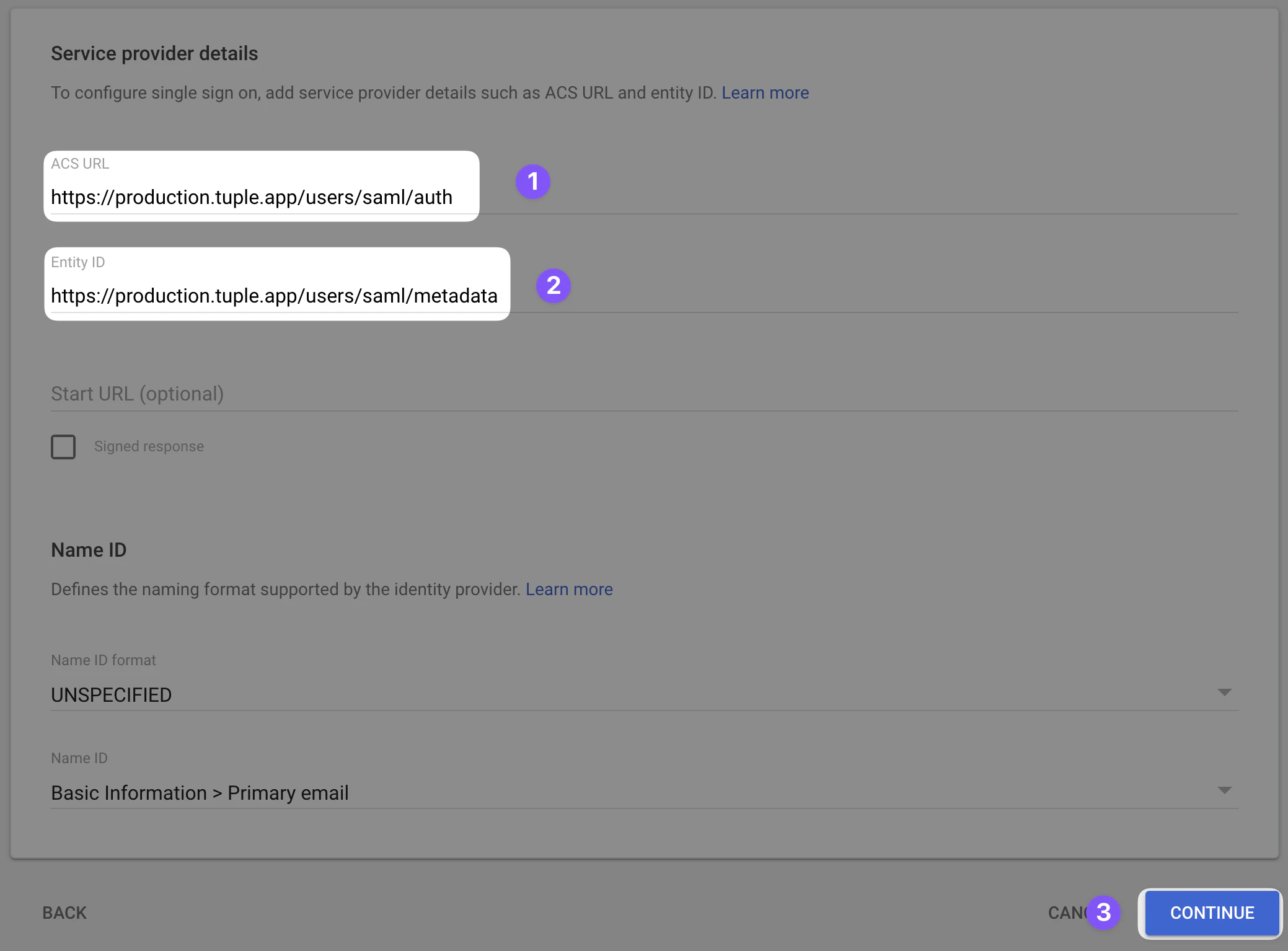
Service provider details
Return to the Google Workspace Admin console and fill in the following fields: